Ivey alumni are on the frontlines in the battle against cybercrime.
In the mid-90s, Victor Keong, HBA ’93, EMBA ’99, approached his manager at Deloitte in Toronto about attending one of the first international firewall conferences, held in San Diego. The manager asked him to do a business case for the conference, and then reluctantly approved the $5,000 expenditure. Within a month of his return, Keong had sold his first Internet security assignment for close to $300,000.
Today Keong is the Security, Privacy & Resiliency Leader with Deloitte & Touche in Singapore. He is one of several Ivey alumni on the frontlines of the war against cybercrime – a war that, by all accounts, is heating up. Massive cyberattacks are now almost daily news items. In late October, an attack shut down major U.S. websites, including Spotify, Netflix, and Twitter. The unauthorized release of data, including emails from the Democratic Party, may have played a role in the results of the U.S. presidential election. It’s estimated that half a million attack attempts are happening globally every minute. The global cost of cybercrime is $100 billion per year, and some say it could reach $2 trillion by 2019.
Once the purview of hackers in dingy basements, cybercrime has become highly organized and very profitable. No surprise then that cybersecurity is a growth industry. But it’s more than a business to the people who make their careers in the field. They see themselves as crime-fighters, warriors, and sheriffs in the Wild West of cybercrime. “We’re called ‘White Hats’ for a reason,” says Jasper Chan, MBA ’05, Director of Product Management at the Cisco Security Business Group in San Jose. “We’re here because we’re trying to do the right thing for society.”
Fighting the Good Fight
At Cisco, cybersecurity is a $1.9-billion business, and the fastest growing division in the company. “It’s a constant battle,” says Chan. “The highly sophisticated and determined adversary is hard to protect against, but at least you can make it harder and harder.”
Chan says digital products are often launched without much thought to security. “If you launch a new offering and then a hacker takes it down, you’re not able to generate the returns promised in your business case. You’re also causing your customers to lose confidence in your brand.” Chan adds that in addition to more traditional attacks, security for the Internet of Things is an emerging challenge.
“It’s the new battleground.” Keong also worries about the vulnerability of mobile devices. For example, by simply sending a text message, a hacker can take control of every aspect of a cellphone, take photographs without the user’s knowledge, and even record a conversation with the user. Mobile Device Management software has become an important part of the security arsenal, he says.
Another new technology to fight cybercrime is User Behavior Analytics (UBA). UBA software is designed to pick up unusual, “out-of-band” activity by users of a system. “A lot of threats are introduced either intentionally or inadvertently by users,” says Keong. “UBA is one of the key things companies need to monitor.”

The hackers only need one way in, whereas we have to defend against all possible threats.” - Linda Berman, HBA ’80
Setting Security Standards
Linda Berman, HBA ’80 (pictured above), worked on a project to install a security system on the mainframe of a Canadian bank in the mid-80s. “I was told that I only had to do it for one year because once the system went in, it would protect everything and there would be no need for security people.” Berman spent the rest of her career working in the field.
Although retired from TD, she is now a Manager with the Payment Cards Industry Security Standards Council, which sets standards for the payment card industry. “We’ve tried to keep pace with the threats ever since the Internet took off in the mid-90s,” she says. “It’s not a fair challenge because the hackers only need one way in, whereas we have to defend against all possible threats.” Berman says that while no one can prevent an intrusion by a determined, well-funded attacker, most breaches can be easily prevented by taking basic security steps, such as good passwords and keeping security software up to date.
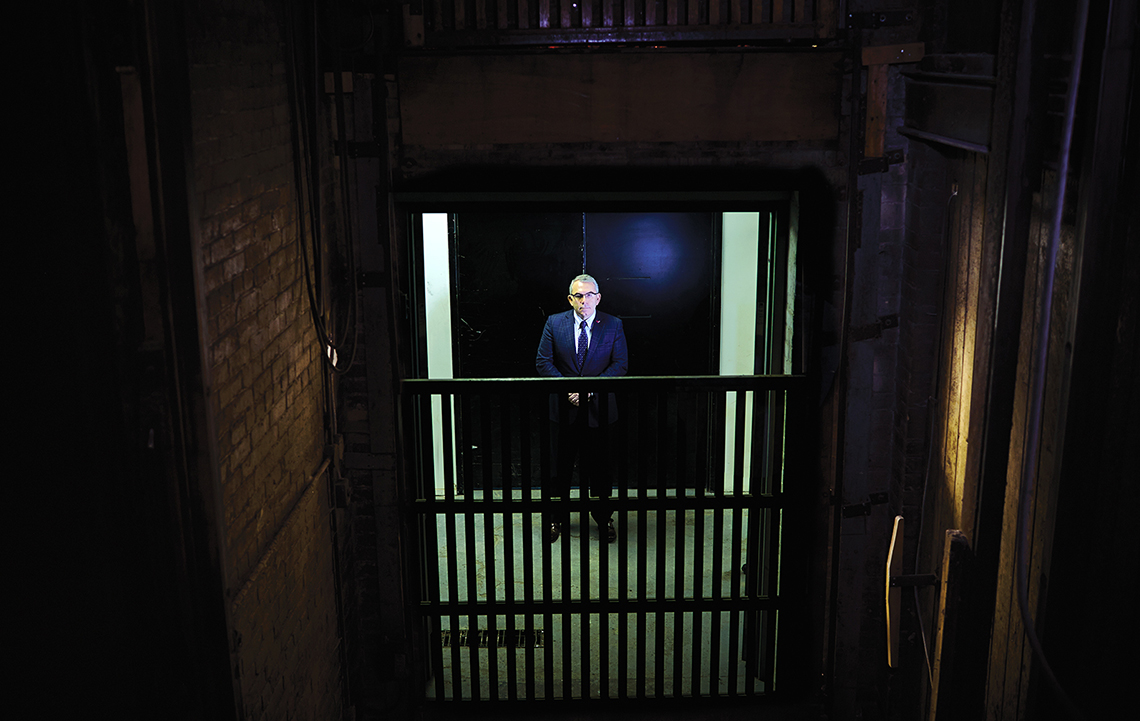
Imad Harb, MBA ’09 (pictured below), started his career as a founding member of NavLink, a managed services company with a focus on security. After six years consulting with Booz & Company, he is now Executive Director at DarkMatter LLC, a startup in cybersecurity based in the United Arab Emirates. “In this business, our adversary is not a machine,” he says. “It’s people as smart as we are. And it’s always evolving – the good guys trying to protect themselves, the bad guys trying to infiltrate.” The expansion of the Internet of Things, wider adoption of Blockchain (the technology behind Bitcoin), and emerging technologies like quantum computing, elevate security challenges to a new level, he says.
It’s essential, Harb says, to educate employees about the risk of cyberattacks and how to prevent them. “The weakest link in any organization is the human factor,” he says. “Putting awareness campaigns and education sessions in place is an important element that most companies ignore.”

Cyber Espionage
Some of the newest adversaries, Harb notes, are nation states. Many have developed unparalleled cyber exploitation and attack technologies that they are beginning to integrate into their national military capabilities. Harb has worked on several national cybersecurity strategies, focusing on both protection and response planning. “We are all going to be attacked at some point,” he says. “How you respond when it happens can make a big difference.”
David Craig, EMBA ’96 (pictured below), is also concerned about the potential of cyberattacks to cripple critical infrastructure at a national level. Craig, who started his career in technical operations in telecom, is now a Partner in Cybersecurity & Privacy with PwC in Toronto. He says more and more countries are developing offensive cyber weapons. “The threat is very real. Once countries launch those weapons, such as in the case of Stuxnet, the software code becomes known and can be used by others for their own dark purposes.” Stuxnet is a malicious computer worm that is believed to have been first developed by the U.S. and Israel to attack Iran’s nuclear program.
Craig believes that businesses and individuals, even countries, must accept that we live in an “era of compromise.” “You have to understand that somebody already has your sensitive data, likely a former employee,” he says. “Have you rehearsed roles for when that becomes public? Does the CEO know what she needs to say? Does the IT team know what they need to do? Being prepared with an appropriate response to data loss is a leading practice that helps maintain, or even build, an organization’s reputation.”
Craig notes that governments around the world are bringing in mandatory breach reporting legislation that will force companies to make cyberattacks more public. “If you’re forced to report every time data has been lost, stolen or accessed in an authorized way,” he says, “you’re likely to improve your duty of care. No one wants to be known as a repeat offender.”
Knowledge Is Key
Chris Kissoon, EMBA ’11, worked in security with VISA before launching Ki33, a cybersecurity consulting firm specializing in payment system risk and security. Kissoon says that credit cards are safer than they’ve ever been for point-of-sale and automated teller machine transactions, thanks in large part to the introduction of chip technology and rigorous security standards. But that may not be enough. “Criminal organizations have long since shifted their focus to the e-commerce and cyber-payment world,” he says. “Innovations in this area are making for a more secure and robust infrastructure. But those responsible for managing these technologies and responding to alerts don’t always have the knowledge to execute on their responsibilities.” He says “critical challenge” programs are crucial to effective cybersecurity.
Kissoon adds that some businesses tend to short-change spending on security. “Security requires money to be spent with no tangible return on investment,” he says. He adds that new attack vectors are being developed and deployed much faster than protective mechanisms are developed. “How do you protect yourself against something you know nothing about? Customized security controls and tools are fast becoming a viable solution, but that requires a commitment to security and brand protection.”
One way to mitigate risk is through insurance. After selling his successful insurance company in 2014, Brian Jones, HBA ’74, launched Ridge Canada, a specialized insurance wholesaler focused on cybersecurity. “I listened to learned people around the world talking about the four greatest non-traditional threats,” says Jones. “They are global warming, pandemics, war, and cyberattacks. Unlike natural disasters, cyberattacks occur every minute, in every industry.” The insurance covers costs such as forensic investigation, crisis management, data restoration, and cyber extortion.
The company’s name honours an association with Tom Ridge, first head of U.S. Homeland Security. Ridge Canada also has a partnership with Cytech, a U.S. cybersecurity firm that provides vulnerability assessment, and forensic and data recovery services for clients. Classmate Hugh MacDiarmid, HBA ’74, is one of the investors and advisers in the new company. “If you’re a director of a larger private company or association, you’re likely asking your CEO if the company is exposed to cyber risk,” he says. “If so, you want to know what he’s doing to limit exposure. For Ridge Canada, that’s a growth opportunity.”
Being prepared with an appropriate response to data loss is a leading practice that helps maintain, or even build, an organization’s reputation." - David Craig, EMBA ’96
No Silver Bullet
Most cybersecurity experts don’t believe a “silver bullet” is on the horizon to protect against sophisticated attacks. “The criminals have to make their ROI too,” Linda Berman says. “If one attack doesn’t work, they move over and try something else. There will never be a one-size-fits-all solution.” Chris Kissoon adds that cyber risk is driven in part by consumer demand for functionality in new software. “You can’t have 100 per cent functionality and 100 per cent security.” If nothing is done to improve security, adds Jasper Chan, fears about cyberattacks will hinder the adoption of digital innovations.
Part of the solution, says David Craig, is to adopt “security by design.” “Organizations are beginning to build privacy and security concepts into their products at the beginning, as opposed to bolting them on at the end.” Craig also believes more cooperation across organizations and sectors will also help combat cybercrime. “It’s all about getting better collectively,” he says. “We have to share information about what an attack signature looks like, so that organizations can better prepare for it.”
Says Kissoon: “There will always be good guys and bad guys. Knowledge is the weapon.”
Photos (Linda & David): Nation Wong
Photo (Imad): Siddharth Siva
Art Direction: Greg Salmela, Aegis